Exploiting Visual Appearance to Cluster and Detect Rogue Software - Prof. Dr. Norbert Pohlmann
Exploiting Visual Appearance to Cluster and Detect Rogue Software | |
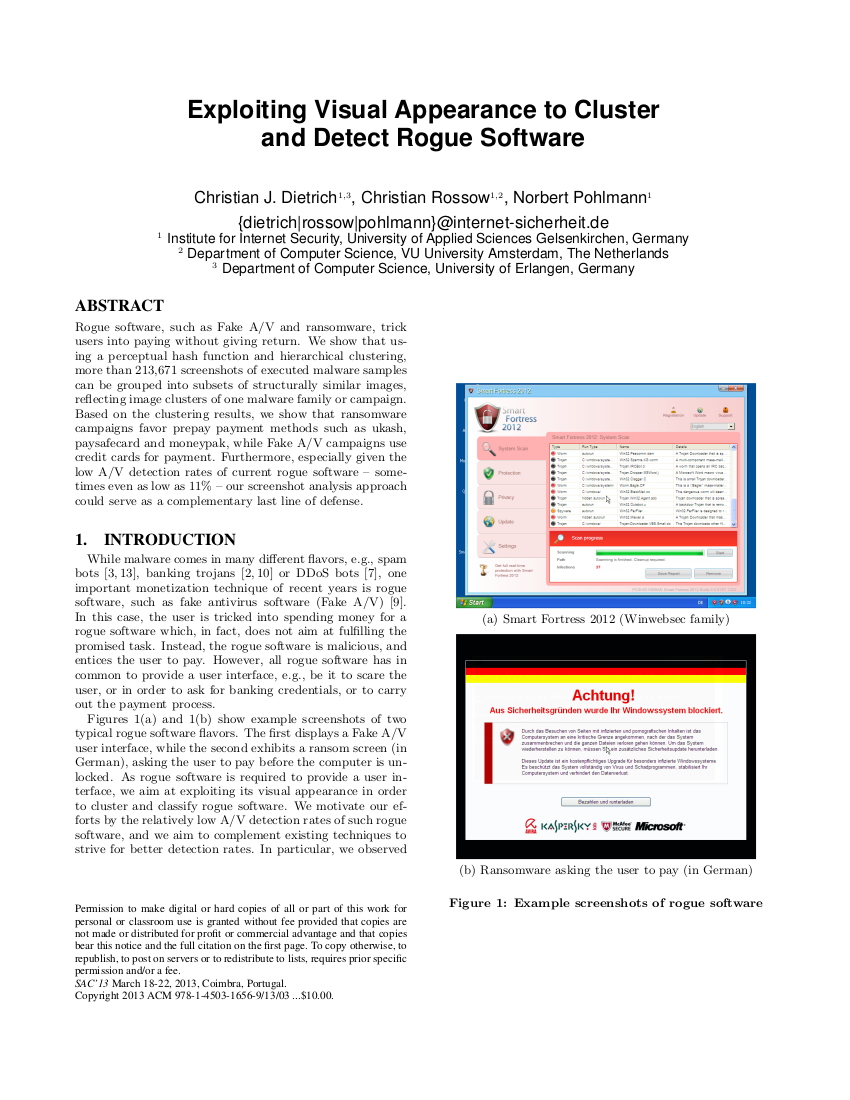
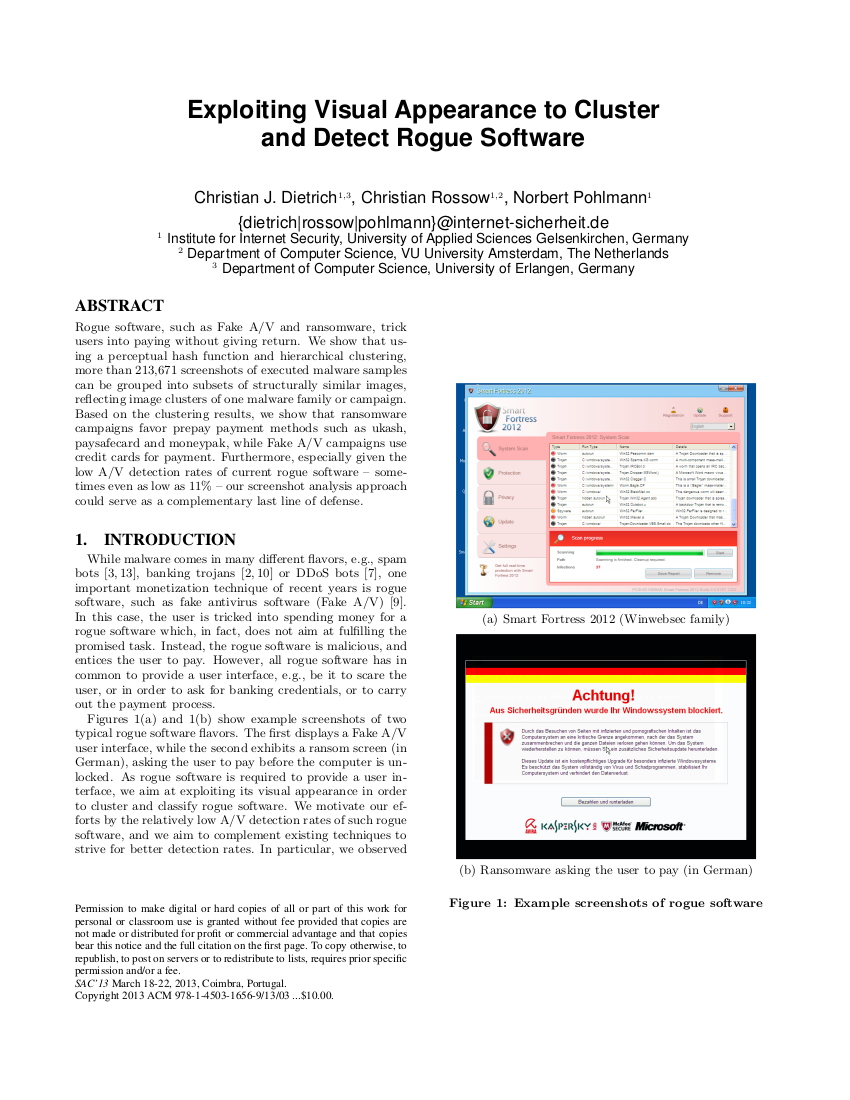 | C. Dietrich, C. Rossow, N. Pohlmann:, Rogue software, such as Fake A/V and ransomware, trickusers into paying without giving return. We show that using a perceptual hash function and hierarchical clustering, more than 213,671 screenshots of executed malware samplescan be grouped into subsets of structurally similar images, reflecting image clusters of one malware family or campaign. Based on the clustering results, we show that ransomwarecampaigns favor prepay payment methods such as ukash, paysafecard and moneypak, while Fake A/V campaigns usecredit cards for payment. Furthermore, especially given thelow A/V detection rates of current rogue software – some-times even as low as 11% – our screenshot analysis approachcould serve as a complementary last line of defense. While malware comes in many different flavors, e.g., spambots, banking trojans or DDoS bots, one important monetization technique of recent years is rogue software, such as fake antivirus software (Fake A/V) [9].In this case, the user is tricked into spending money for arogue software which, in fact, does not aim at fulfilling the promised task. Instead, the rogue software is malicious, andentices the user to pay. However, all rogue software has incommon to provide a user interface, e.g., be it to scare theuser, or in order to ask for banking credentials, or to carryout the payment process. Figures 1(a) and 1(b) show example screenshots of twotypical rogue software flavors. The first displays a Fake A/Vuser interface, while the second exhibits a ransom screen (in German), asking the user to pay before the computer is unlocked. As rogue software is required to provide a user interface, we aim at exploiting its visual appearance in orderto cluster and classify rogue software. kostenlos downloaden |
 | |